Phishing attacks steal personal information by baiting you into doing something, like clicking a link or entering your username and password. Phishing comes in many forms—emails, texts and phone calls to name a few. Phishing attempts may look like they are from Florida State University—often IT Services or professors—but don't take the bait!
Phish Tank
Here phishy, phishy! Check the Phish Tank for a list of the latest known phishing emails targeting FSU.
Types
Spear Phishing
Spear phishing is a well-researched and targeted attack. These messages often appear as an email from a trusted person or entity and may include personal details about the victim to make the email seem believable.
Vishing
Vishing is an attempt to steal information via a phone call or voicemail and is often a prerecorded message. These calls pretend to be from a reputable company and may even spoof the caller ID to look legit. Common vishing scams include tax scams and unsolicited loan offers.

Smishing
Smishing is like phishing, but instead of being targeted over email, the attacks come as texts or direct messages over social media. These attacks can be very convincing and range from bank notifications to package shipping updates.

Whaling
A whaling attack is a method cybercriminals use to masquerade as a senior player at an organization and directly target other VIPs within the organization. These scams use a "big fish" to reel you in. The aim is to steal money or sensitive information or gain access to computer systems at an elevated level for criminal purposes.
Warning Signs
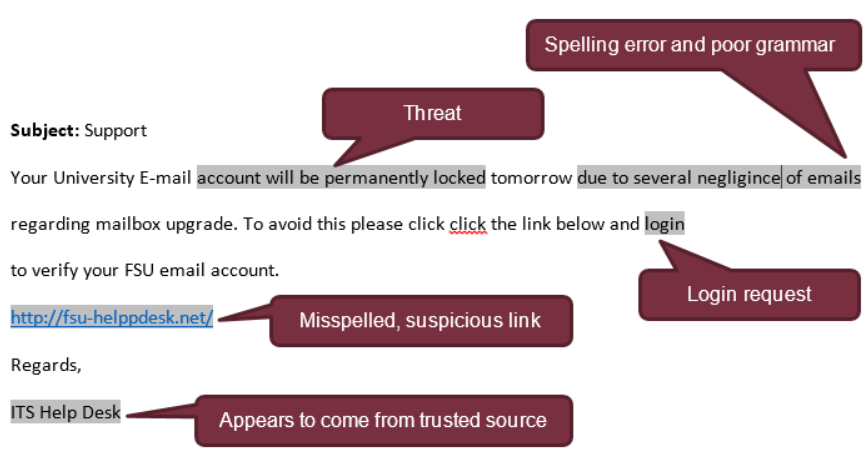
Suspicious Links
A link. That is usually where it all starts. Always stop and think before clicking email and website links. Keep in mind that you can make anything a hyperlink. Even though the text might say www.fsu.edu, there is no guarantee that you will end up on that site. Hover over or long tap a link to display the actual URL. This goes for QR codes too. In general, if you do not know who the link came from, do not click it.
Username and Password Request
FSU or any legitimate company—banks, insurance companies, social media accounts—will never ask for your username and password in an email or phone call. Never reply to an email or phone call asking you to provide your username, password or other sensitive information. And never enter your password on a site you accessed via a link in an email from an unknown sender.
Display Name Spoofing
Unlike other spam emails, display name spoofing involves a malicious email sent from an email address on a valid domain, such as Gmail, but sets the display name to appear from someone within the organization, such as a trusted professor, fellow student or the university president.
Spelling Errors and Bad Grammar
Most cybercriminals did not get an "A" in English class. At FSU and other reputable companies, professional copy editors and communication specialists proofread emails to ensure everything is top quality before sending. If you see ghastly spelling errors or cringe-worthy grammar, it is likely a phishing message.
Threats
Cybercriminals often try to bully you into acting by threatening you will lose something if you do not respond immediately. Common threats include "your email account will be closed" or "your device is infected." Cybercriminals aim to make the situation seem dire so the victim, you, feel obligated to act and provide personal information. FSU will never require you to sign in to keep your account.
Spoofed Websites
Does something look a bit off? If you click a link in an email, pay attention to the page you land on. Scam artists often spoof trusted websites, making their phony site look very similar to the real thing. Pay particular attention to the URL; if it is anything other than expected, close the page immediately.
Tips
Think before clicking email and website links, and never click a link that looks suspicious
Before clicking, hover over or long tap a link to display the actual URL and see if it is linking to a reputable website
Instead of clicking, type website addresses in your browser to access sites directly
Be skeptical of messages that require "immediate action" or threaten you will lose something
Do not open attachments you are not expecting, especially ZIP files, and never run .EXE files
Avoid providing personal information over the phone, especially from an unsolicited call
Never send credit card numbers or other sensitive information via email
If it seems too good to be true, it probably is
What to Do
If you have been targeted by phishing at FSU:
- Call the ITS Service Desk to verify whether an email claiming to be from FSU is real: 850-644-4357
- Forward phishing emails to abuse@fsu.edu
- If you believe your account has been compromised, follow these instructions to secure your account
If you have been targeted by phishing at home:
- Delete the email or message
- If you believe your account has been compromised, follow these instructions to secure your account
Resources
Phishing Attacks
LinkedIn Learning course on real-world examples of phishing attacks and how to prevent them
Phishing IQ Test
Test your ability to spot fraudulent emails with real examples from common phishing attacks